6.2. Using seaudit for Audit Log Analysis
Troubleshooting policy violations can mean wading through convoluted audit logs. The seaudit application is designed to help you read, sort, and query your SELinux audit messages. In addition, seaudit-report generates formatted reports of SELinux messages from the audit log, useful for reports such as those generated by logwatch. The information you gather helps you in analyzing problems and creating solutions.
It is necessary to have super-user privileges to run seaudit, because it looks into system logs. For this reason, /usr/bin/seaudit is a symlink to consolehelper, as well as a program accessible directly by root at /usr/sbin/seaudit.
You can choose which log and policy file to use when starting the application, for example, seaudit -l /path/to/log -p $SELINUX_SRC//policy.conf. seaudit can use both binary and source policy files.
Although simpler than the related apol, seaudit has more capabilities than are covered by this section. This section focuses on how to accomplish basic tasks using seaudit. For more information about what seaudit is, read the online documentation at /usr/share/doc/setools-<version>/seaudit_help.txt, which is also available from the Help menu in seaudit.
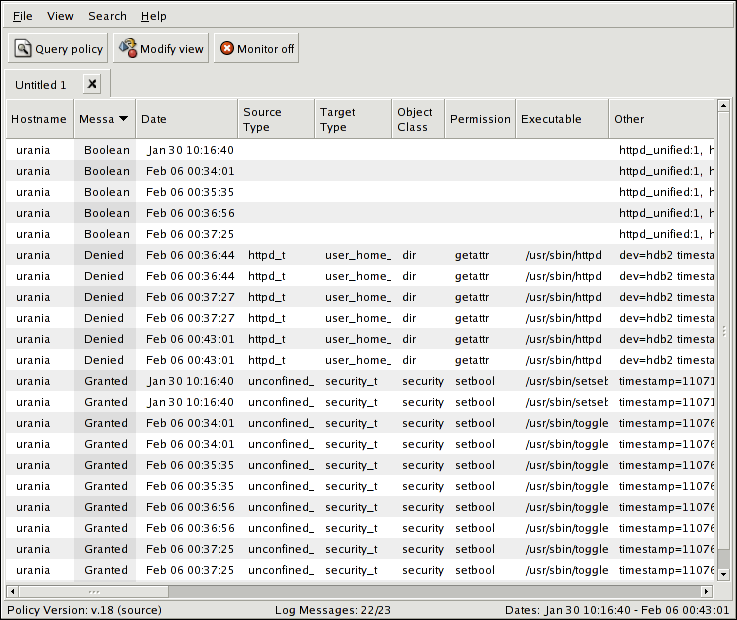
Figure 6-1 shows seaudit displaying the audit log with several different kinds of messages displayed. The Other column is where the timestamp and serial number are displayed.
6.2.1. Arranging Your Views in seaudit
There are several features to seaudit that make it easier to work with the audit messages. The first happens simply by loading a log into seaudit. You find only the SELinux log entries are displayed, with all of the data fields in the log message divided into columns. Clicking on the top of a column sorts the records by that column.
If you want real time monitoring of the log file, click on Monitor <off> to toggle the log watching. Clicking on the button again turns monitoring off.
Column sorting only supports one level, meaning you can only sort by a single column. The Other column is not a sort option. In order to sort by more fields, use the filter capability through View => Modify or the Modify view button. The window that pops up manages your filters, letting you control, edit, save (Export), and load (Import) the filters, as well as save the entire view:
The View window is where you create filters to help organize and analyze log entries. Clicking on the Add or Edit button brings up the Edit filter window:
From here you can set filters to sort on source context, target context, object class, IP address, port, interface, source executable, path to the target, and hostname. Criteria matching is all or any. When you choose a context for a filter, such as under Target Type clicking on Types:, the Select Target Types window pops up with the available types, as shown in Figure 6-4. These types are just the ones that are represented in the audit logs:
Instead of picking exact types, you can use wildcard and related matching mechanisms, collectively called globbing. The techniques are detailed in Table 6-2. All globbing expressions are case sensitive.
| Glob Type | Behavior |
|---|---|
| ? | Matches any single character. For example, a?c matches abc, aqc, a1c, and so forth. |
| * | Matches one or more characters. For example, reg* matches regular, regex, regexp, and so forth. |
| [...] | A list of characters searched for in a particular position. For example, a[bde]c matches abc, adc, and aec. The brackets cannot be empty. |
| [x-y] | This searches for the range of specified characters. The range is [<beginning_of_range>-<end_of_range>]. You can specify more than one range. For example, h[a-z]ly matches any word that begins with an h and ends with an ly and has only one alpha character in between, such as hrly, hmly, and hlly. Another example is 1[2-46-9]0, which gives you every combination except 150. The range is inclusive, for example, [a-c] includes a, b, and c, and not just b. |
| [!...] | When the ! opens the expression, it signifies a complement of the character or range that follows. This globbing pattern uses a list. Complementation is a mathematical term, and in this cases means, "not the character or range that follows." For example, 1[!4-6]0 matches any combination from 110 to 190 except 150, that is, "not the number that is in the range of 4 to 6." The range is not inclusive, which means [!4-6] can only mean !5, and does not mean !4, !5, !6. |
| ^ $ | The caret and the dollar sign signify that you want to anchor the search so that the string itself is searched for without anything before or after it. For example, ^httpd_suexec$ is searching for just httpd_suexec and not httpd_suexec_exec_t. To open up one end of the search, replace the ^ or $ with a different globbing mechanism. |
Table 6-2. Globbing Expressions in seaudit
You can combine the globbing expressions for increased capability. For example, h[a-z]*ly finds patterns such as hzfooly, hazily, hardly, hardily, and so forth.
All of these search functions are described in additional detail with examples in the seaudit help documentation. This is viewable through Help => Help, which opens the file from /usr/share/doc/setools-<version>/seaudit_help.txt.
You can open multiple views into the same log by opening additional tabs. View => New creates a new view of the log in a different tab, and you can sort and filter this log. This helps when you are sorting through complex denials trying to find root causes.
Back in the main audit log view window, you can get more information on each individual log entry. By double-clicking on the entry, or right-clicking and choosing View Entire Message, the individual log entry is opened in a pop-up window. You can also get to this view through View => View Entire Message, which displays the selected message. If more than one message is selected, the top one is displayed.
There are two additional right-click commands. Query Policy Using Message opens a Query Policy window with the search parameters populated with details from that single message. This is explained in Section 6.2.2 Searching and Querying in seaudit. The last right-click menu option is Export Message to File, which lets you save a log file containing the single message.
6.2.2. Searching and Querying in seaudit
A more complex method of analyzing your audit messages is to look for pertinent rules in the policy. You can use the elements of the denial message in the queries. The query tool in seaudit is similar to the TE rules query capability in apol. This is helpful for conducting SELinux work involving log and policy analysis.
Clicking on Query policy or Search => Query policy opens the Query Policy window. If you have a log highlighted, the fields are pre-filled with the log entry details.
Full regular expression support is enabled for the Query policy window. The globbing expression behavior used in the Modify view filtering is not available.
In the Query policy window, the policy.conf tab displays the currently active policy.conf from the active policy. You need to have a policy file loaded in order to query the policy.
If you do not have the policy source installed or the file $SELINUX_SRC/policy.conf is not present, you need to manually load a different policy file through File => Open policy. For example, you can use the binary policy in $SELINUX_POLICY/policy.<XY>, or a binary or source policy file from another system. However, if you use a binary policy, the policy.conf tab does not appear.
With the policy loaded into the policy.conf tab, your query results include a number in parenthesis, for example, (3577). These numbers are hyperlinks to the corresponding line number in the policy.conf file. Clicking on the hyperlink takes you directly to the location in the policy.conf tab.
In the query fields, checking Include indirect matches ensures that you are searching by the source and target values as well as any attributes that contain types identified by those same regular expressions. Unchecking a set of fields, such as Target type regular expression, disables that set from the query. This opens the query up to finding, for example, every connection from the source to every target. To truly open the search, you can remove the Object class query field.
6.2.3. Using seaudit-report to Generate Reports
The utility seaudit-report is useful for generating reports of SELinux-related log activity. The command lets you specify the incoming log source, either from files or STDIN, and output to a file or STDOUT as text or styled HTML. By piping through seaudit-report using STDIN and STDOUT, you can use this utility to generate automatic reports that can be sent via email or posted on an Intranet page. The format is designed to be used by programs such as logwatch.
You can customize the reports generated by seaudit-report in two ways. Visual customization is first done in the layout of the configuration file, which determines which reports are nested where. This continues if you use HTML output. The cascading stylesheet (CSS) at /usr/share/setiils/seaudit-report.css can be used directly or modified to fit your needs.
Another customization is through the seaudit-report report configuration file at /usr/share/setools/seaudit-report.conf. This file details how to enable and disable the standard report fields, as well as how to include customized views that have been saved from seaudit. Here is the default configuration XML:
<seaudit-report title="SEAudit Log Report">
<standard-section id ="Statistics" title="Log \
Statistics"></standard-section>
<standard-section id ="PolicyLoads" title="Policy \
Loads"></standard-section>
<standard-section id ="EnforcementToggles" \
title="Enforcement mode toggles"></standard-section>
<standard-section id ="PolicyBooleans" title="Policy \
boolean changes"></standard-section>
<standard-section id ="AllowListing" title="Allow \
Listing"></standard-section>
<standard-section id ="DenyListing" title="Deny \
Listing"></standard-section>
</seaudit-report> |
You can remove reports by removing the XML tag-set for it, and you can put custom views obtained from saved views in seaudit into a <custom-section>. Refer to the installed documentation at /usr/share/setools/seaudit-report.conf for a more detailed explanation of usage.
This shows portions of a report output from seaudit-report, rendered directly to plain text:
# Begin
# Report generated by seaudit-report on
# Sun Feb 6 16:20:01 2005
Title: SEAudit Log Report
Log Statistics
--------------
Number of total messages: 15
Number of policy load messages: 2
Number of policy boolean messages: 2
Number of allow messages: 4
Number of denied messages: 8
Policy Loads
------------
Number of messages: 2
Feb 06 17:32:37 urania kernel: security: 3 users, 4 roles, \
316 types, 20 bools
Feb 06 17:32:37 urania kernel: security: 53 classes, 9815 rules
Enforcement mode toggles
------------------------
Number of messages: 0
Policy boolean changes
----------------------
Number of messages: 2
Feb 06 19:44:32 urania kernel: security: committed booleans: \
{ httpd_unified:1, httpd_enable_cgi:1, httpd_enable_homedirs:1, \
httpd_ssi_exec:1, httpd_tty_comm:0, httpd_disable_trans:1, \
dhcpd_disable_trans:1, mysqld_disable_trans:0, \
named_disable_trans:0, named_write_master_zones:0, \
nscd_disable_trans:0, ntpd_disable_trans:0, \
portmap_disable_trans:0, postgresql_disable_trans:0, \
snmpd_disable_trans:0, squid_disable_trans:0, \
syslogd_disable_trans:0, winbind_disable_trans:0, \
ypbind_disable_trans:0, allow_ypbind:1 }
...
Allow Listing
-------------
Number of messages: 4
Feb 06 19:44:32 urania kernel: audit(1107747872.351:7619987): \
avc: granted { setbool } for pid=3803 exe=/usr/sbin/togglesebool \
scontext=root:system_r:unconfined_t \
tcontext=system_u:object_r:security_t tclass=security
...
Deny Listing
------------
Number of messages: 8
Feb 06 19:42:45 urania kernel: audit(1107747765.871:7550947): \
avc: denied { getattr } for pid=2479 exe=/usr/sbin/httpd \
path=/home/auser/public_html dev=hdb2 ino=921135 \
scontext=user_u:system_r:httpd_t \
tcontext=system_u:object_r:user_home_t tclass=dir
Feb 06 19:42:45 urania kernel: audit(1107747765.872:7550962): \
avc: denied { getattr } for pid=2479 exe=/usr/sbin/httpd \
path=/home/auser/public_html dev=hdb2 ino=921135 \
scontext=user_u:system_r:httpd_t \
tcontext=system_u:object_r:user_home_t tclass=dir
...
# End |